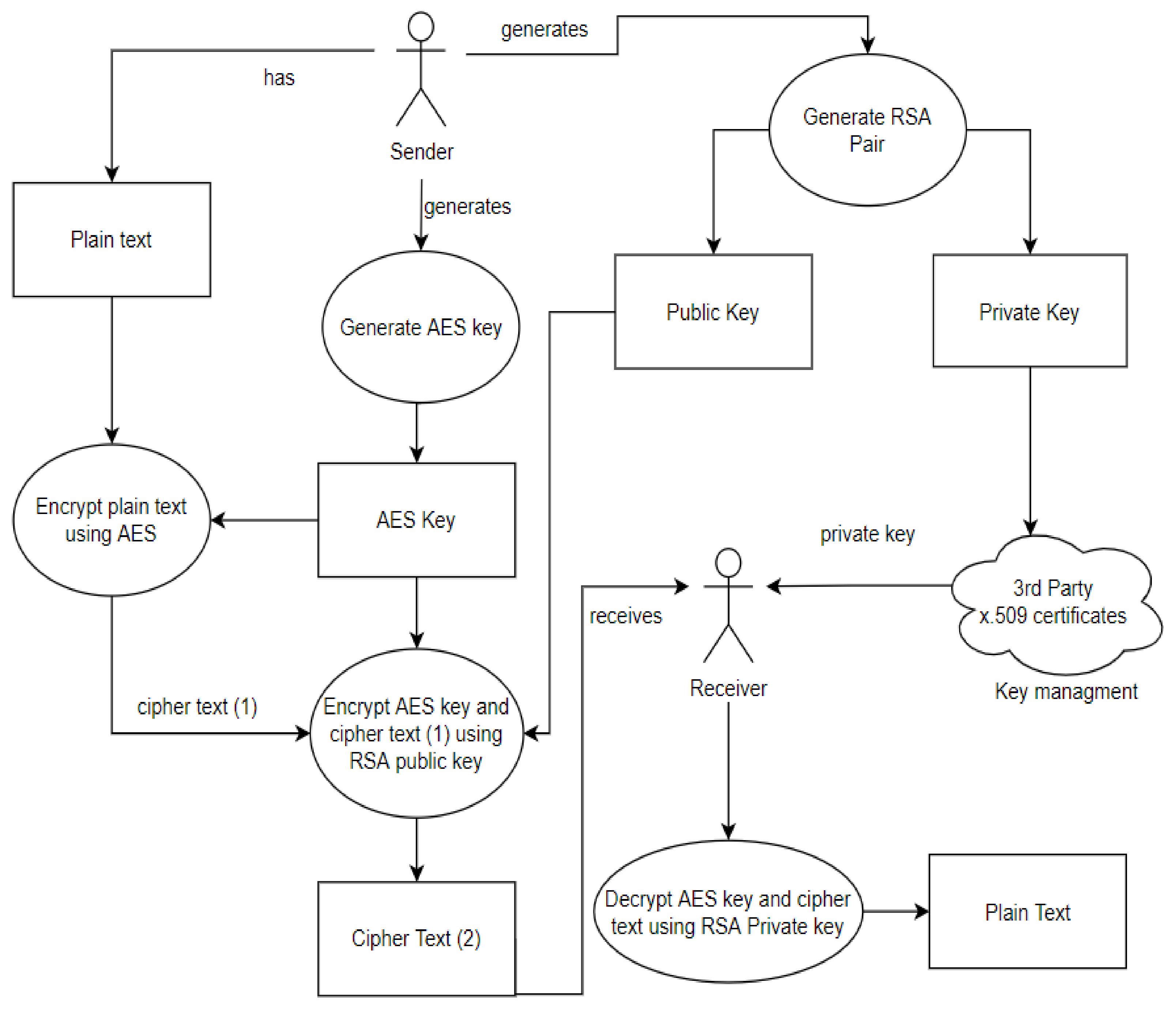
Sensors | Free Full-Text | A Dynamic Four-Step Data Security Model for Data in Cloud Computing Based on Cryptography and Steganography
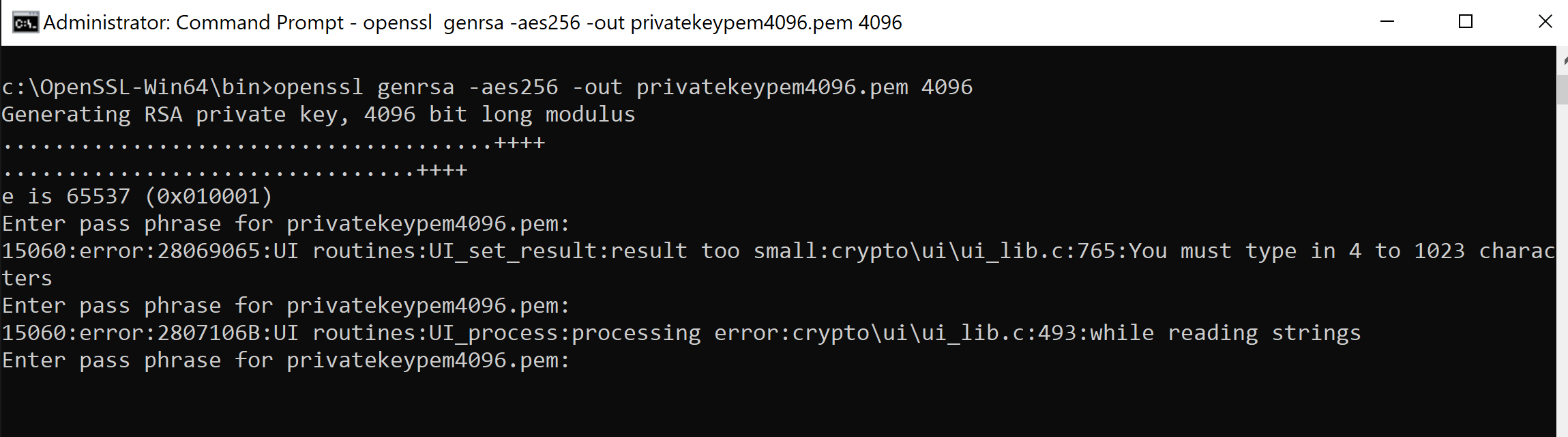
OPENSSL : How to make a private key using AES 256 | University of South Wales: Cyber University of the year: Four years running: 2019, 2020, 2021, 2022