
Drones | Free Full-Text | An Intrusion Detection Model for Drone Communication Network in SDN Environment

The Bot Stops Here: Removing the BotNet Threat - Public and Higher Ed Security Summit - Eric Vanderburg | PPT
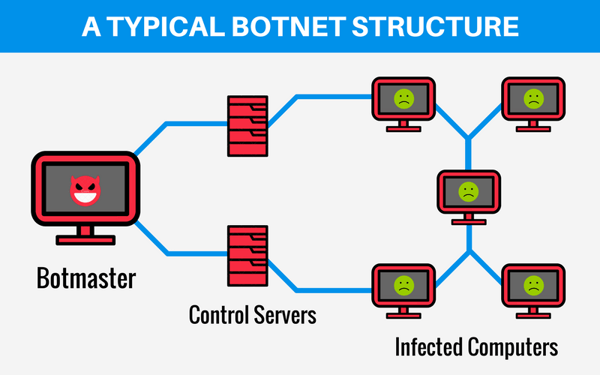
Symmetry | Free Full-Text | Machine Learning-Based Botnet Detection in Software-Defined Network: A Systematic Review

The architectural design of AA-Dense RNN based Botnet attack detector... | Download Scientific Diagram

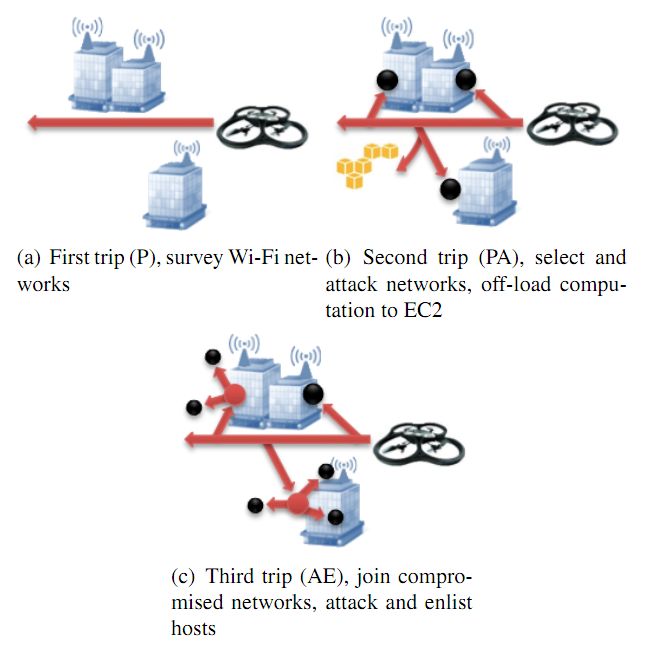
What happens if a hacker 'hijacks' all those drones Amazon wants to put in the sky? — bobsullivan.net
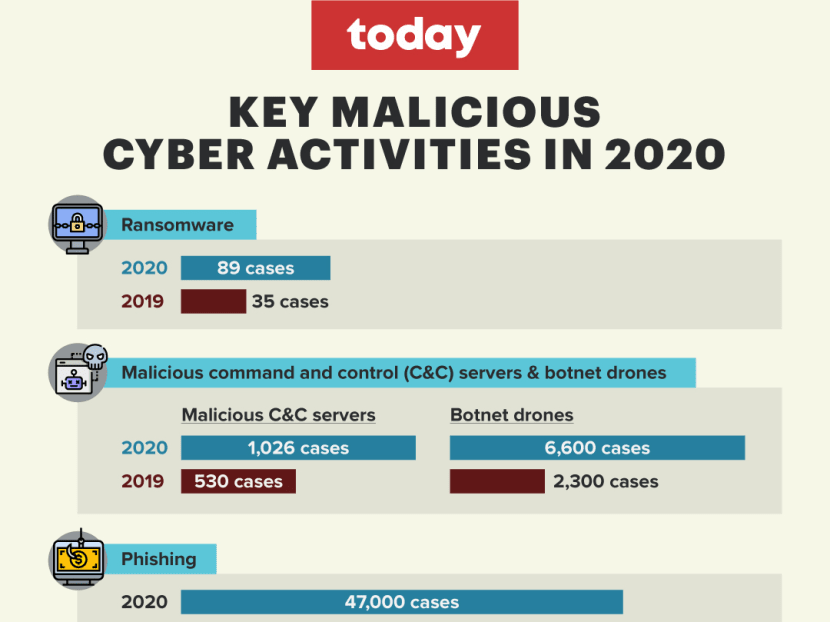
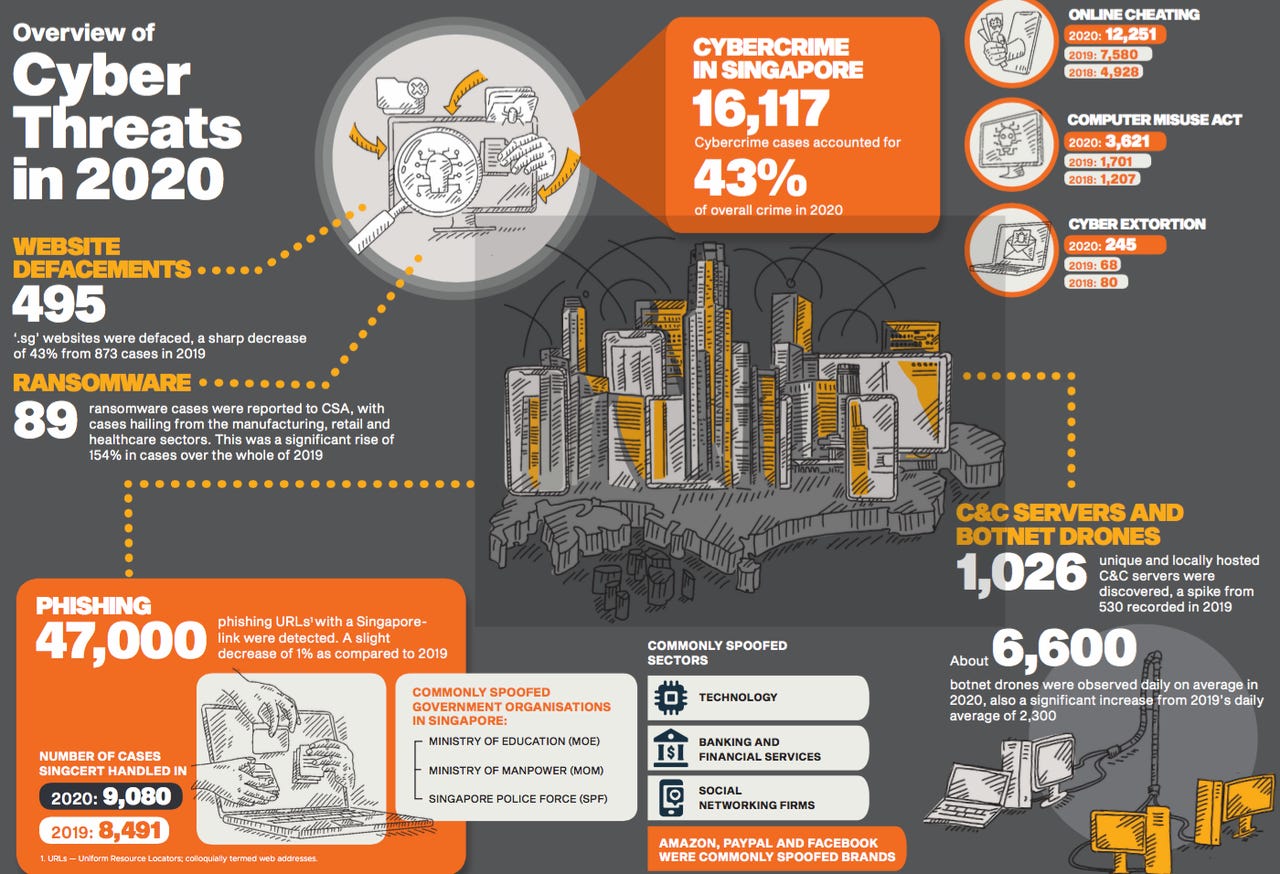
Surge in Singapore-linked 'botnet drones', used by cyber criminals to hack into household devices: Report - TODAY
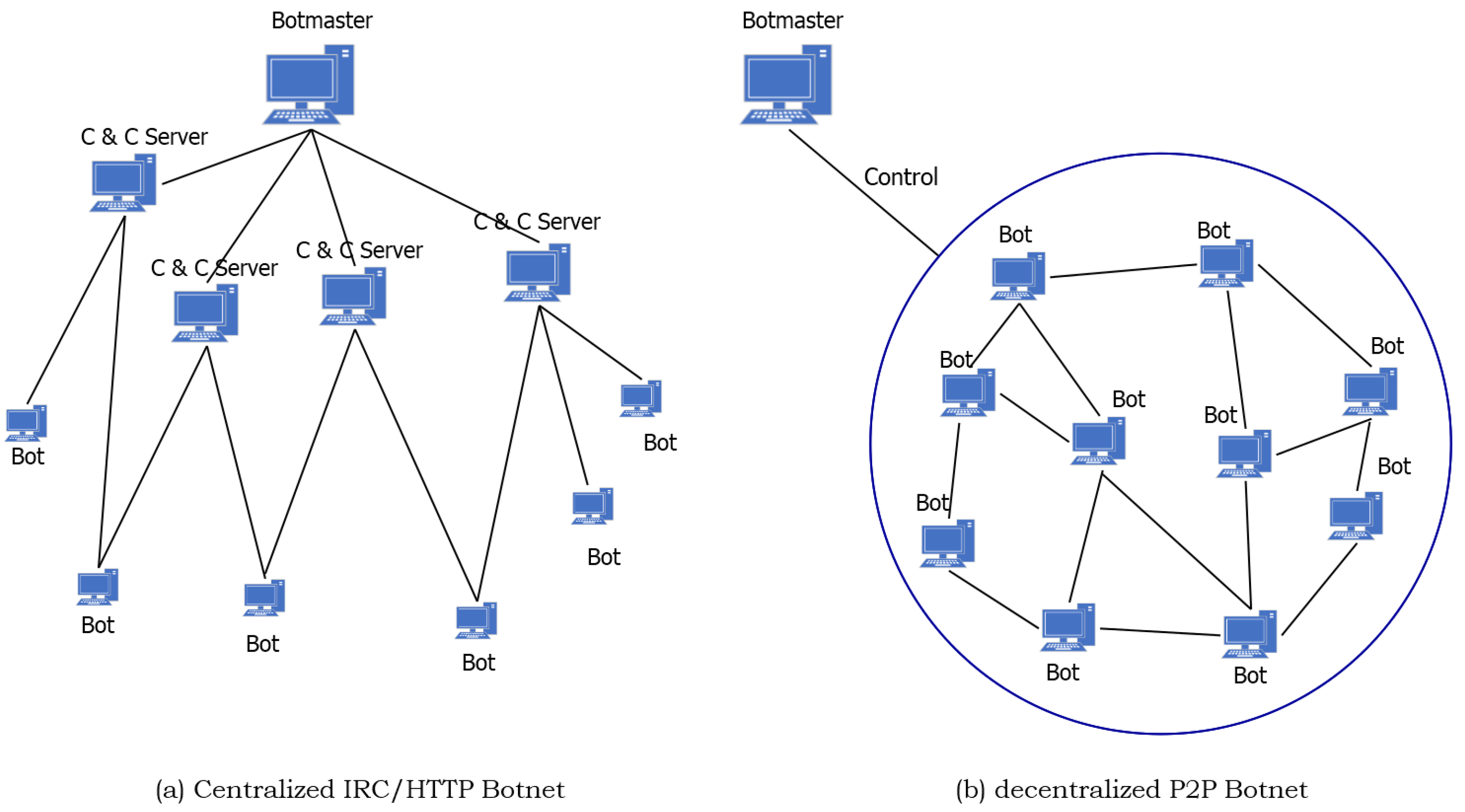
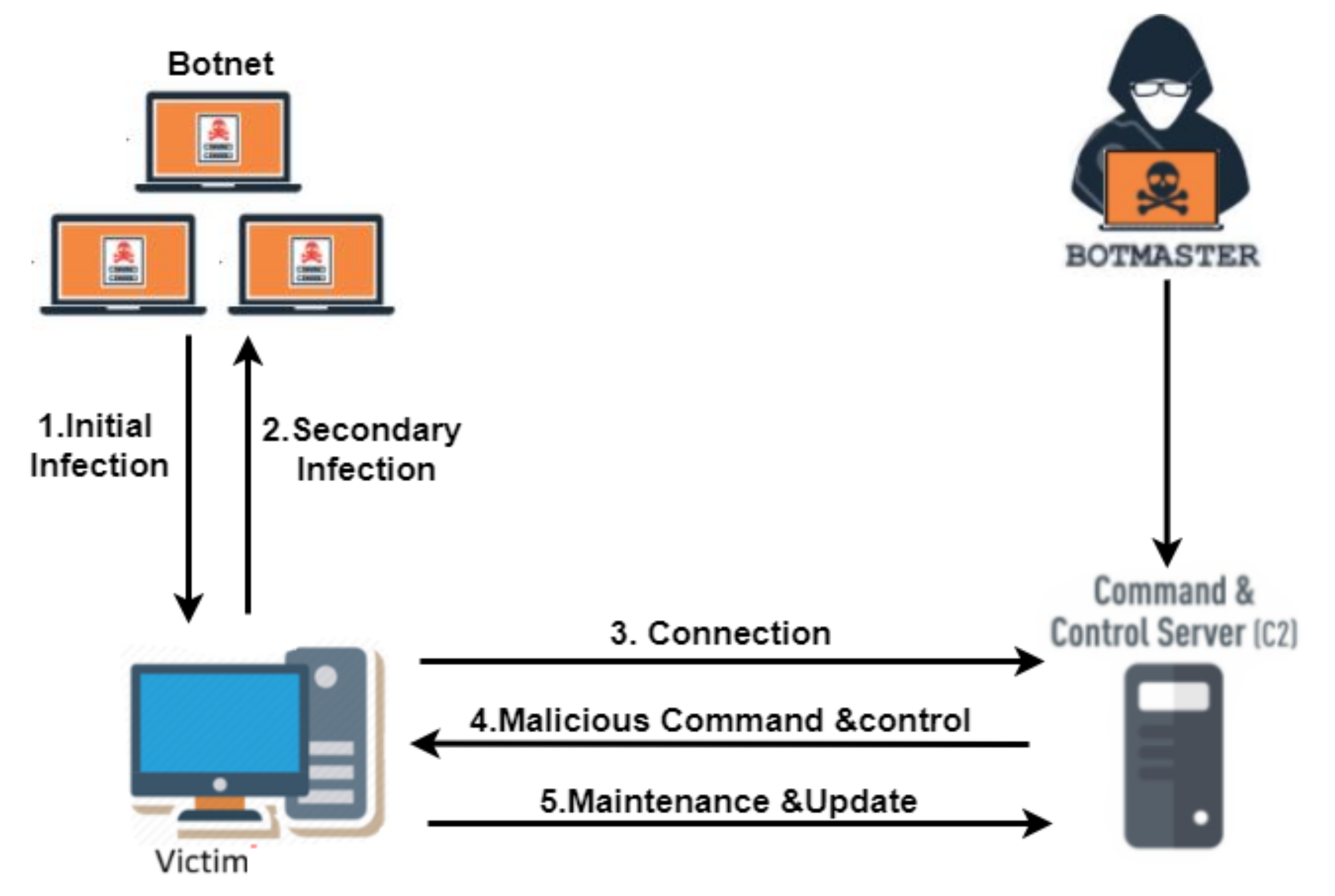
Applied Sciences | Free Full-Text | An Adaptive Multi-Layer Botnet Detection Technique Using Machine Learning Classifiers
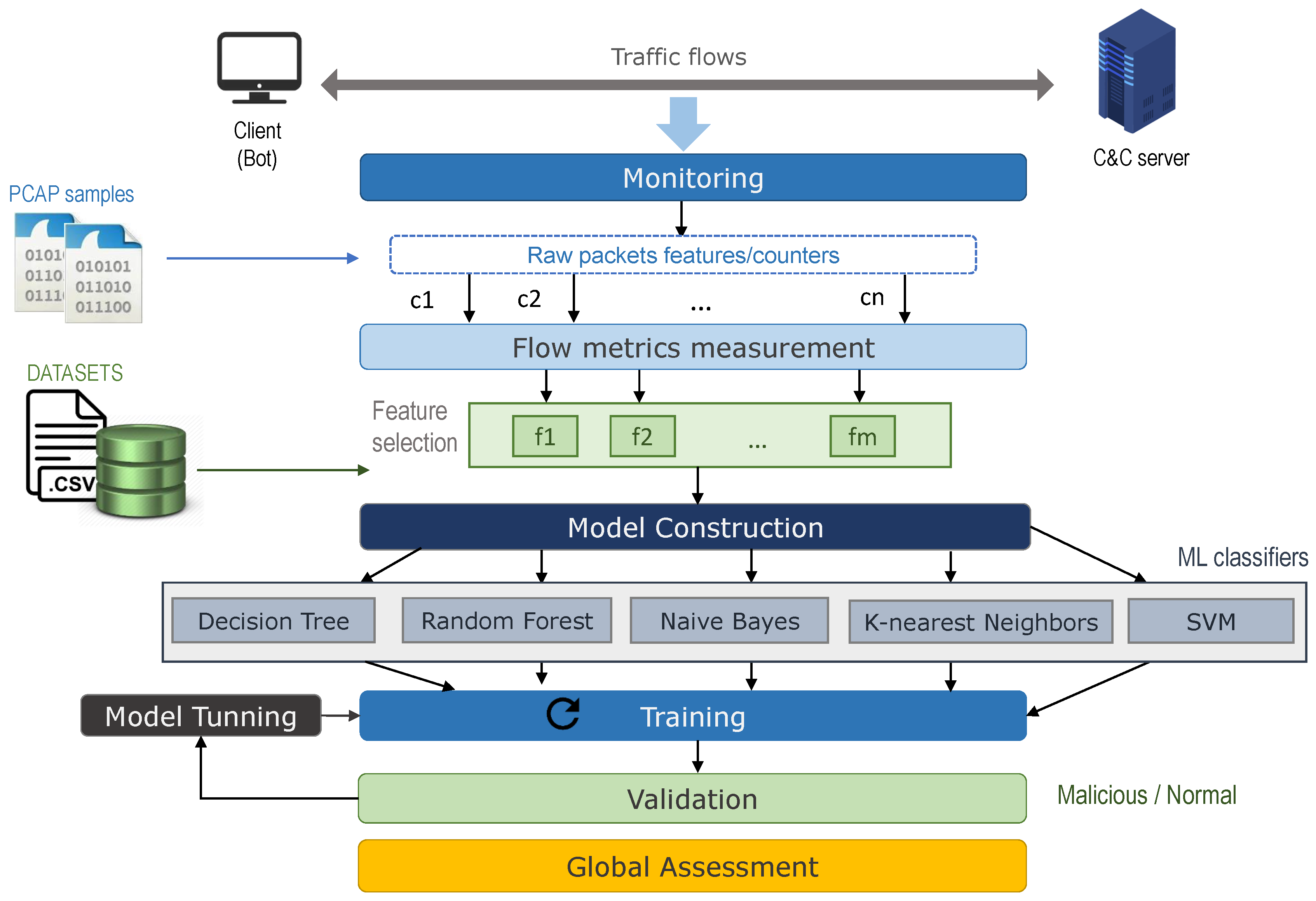
Sensors | Free Full-Text | Benchmark-Based Reference Model for Evaluating Botnet Detection Tools Driven by Traffic-Flow Analytics

The four main botnet topologies as modelled in NS3/NSNAM (A. Scenario... | Download Scientific Diagram

Surge in Singapore-linked 'botnet drones', used by cyber criminals to hack into household devices: Report - TODAY

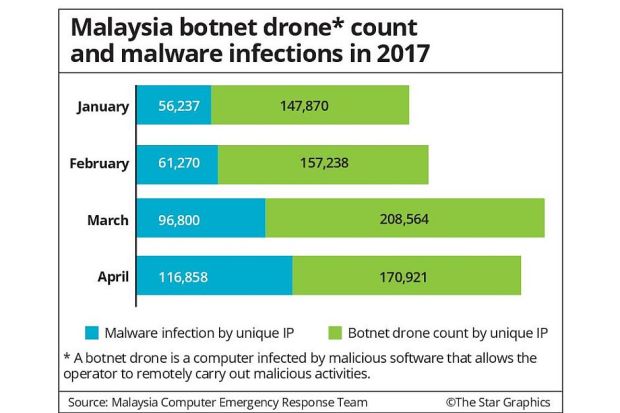
![Botnet Drones Attack in Malaysia[14] The record universal cases... | Download Scientific Diagram Botnet Drones Attack in Malaysia[14] The record universal cases... | Download Scientific Diagram](https://www.researchgate.net/publication/283257776/figure/fig1/AS:289115225509893@1445941849529/Botnet-Drones-Attack-in-Malaysia14-The-record-universal-cases-performed-by-botnets-are.png)






![Botnet Drone! by Poofdra -- Fur Affinity [dot] net Botnet Drone! by Poofdra -- Fur Affinity [dot] net](https://d.furaffinity.net/art/poofdra/1615251090/1615251090.poofdra_unknown__7_.jpg)